On September 15, 2014 Cisco has made an End-Of-Sale and End-Of-Life announcement for their Cisco Jabber for TelePresence (aka Movi) version 4.8 and later: http://www.cisco.com/c/en/us/products/collateral/collaboration-endpoints/jabber-video-telepresence-movi/eos-eol-notice-c51-732787.html R.I.P. Movi…
Author: alex
Cisco Jabber 9.6.3 for iPhone/iPad Is Here
Finally, Cisco has released an update to their Cisco Jabber client for Apple iOS devices and Cisco Jabber 9.6.3 is now available from the App Store. This version fixes the CSCuo85316 and CSCup28228 bugs, both of which were affecting users’ ability to connect their Jabber to CUCM/CUPS via Expressways. MRA is now fully functional across all popular platforms: Windows/Mac, Android and [finally] Apple iOS family devices.
Enabling Medianet’s Metadata on Endpoints Running TC6.0 Through TMS
If you would like to bulk-enable Medianet’s metadata on Cisco endpoints running software TC6.0 and higher, you can do so using TMS Configuration Template with a custom API command. Here’s how:
- Navigate to Systems > Configuration Templates > Configuration Templates.
- Create new configuration template or edit an existing one.
- Click on ‘Select Advanced Settings’ tab and use the filter to search for ‘custom configuration’ for ‘Cisco TelePresence TC Endpoints’:

- Select the ‘Custom Configuration’ setting and click ‘>’ to add it to the settings list.
- Switch to ‘Template Settings’ tab and paste the following string in the ‘Custom Configuration’ line:
<Configuration> <Experimental item="1"> <NetworkServices item="1"> <Medianet item="1"> <Metadata item="1">On</Metadata> </Medianet> </NetworkServices> </Experimental> </Configuration>
- Save the template. You’re done!
Test the configuration by applying the new template to a single endpoint and confirm that there were no errors and the setting has been changed successfully.
VCS Alarm: ‘RxPLIManager Line: 54’
We had one of the VCSes raise an alarm a few days ago that reads as follows:
An unexpected software error was detected in ivy[14753]: SIGABRT (tkill(2) or tgkill(2))
A closer look into details reveals the following:
| Stack | 0x0000000000c2c407 RxPLIManager ppcmains/ivy/b2bua/offeranswer/sdp/RxPLIManager.cpp:54 0x00007f032c66f2a5 (InstructionPointer) 0x00007f032c9fab30 (__builtin_return_address(0)) |
Cisco has confirmed that it is a new bug with X8.1.1. The application automatically restarts, so there is no need to do anything other than acknowledge the alarm for the notice to go away.
User accounts are automatically disabled in CWMS 2.0 MR4
Update #2 07-18-2014: A hotfix cisco-webex-meetings-server-2.0.1.416.B.iso has been released for customers who are affected by the defect CSCup62113. The hotfix is available via special download only; to obtain access to it, please contact Cisco TAC.
Update #1 07-08-2014: Apparently, another outcome of the bug is that the Personal Conferencing accounts have been removed from all user profiles after users were temporarily deactivated in CWMS. There is a way to re-enable the old host/participant access codes if a user creates a new Personal Conferencing account (regardless whether the same or a new PIN is specified). The old Personal Conferencing host/access codes will not show up in the users’ profile or WebEx Productivity Tools in Outlook.
So I have upgraded our CWMS 2.0 environment to the latest maintenance release (MR4 or 2.0.1.407). Everything went well and the systems tested successfully post the upgrade. Time to remove pre-upgrade snapshots of your CWMS VMs (don’t ever forget to do this, as snapshots left behind do have an adverse effect on VM performance) and call it a night. Well, it turned out that the newest maintenance release is bugged and this time it is a big one. If you haven’t upgraded to the latest maintenance release, but plan to do it sometime soon, you’d likely want to reconsider. Read on…
So I have learned today that all but two of my 5000+ users were deactivated in CWMS with a status “disabled on LDAP” (which, of course, isn’t true). Users can still authenticate with the CallManager (with which CWMS synchronizes), so directory synchronization with LDAP and LDAP authentication isn’t a problem. Turns out, CWMS would disable any user whose record hasn’t been updated in the CallManager within the past few weeks (8 to be precise, as claimed by a Cisco TAC engineer). There is no patch or hotfix available at this point, but a workaround is as follows:
- Make a change (any change) for the affected end user object(s) in the CallManager (you’d likely want to make the changes in bulk using BAT).
- Synchronize the users in CWMS
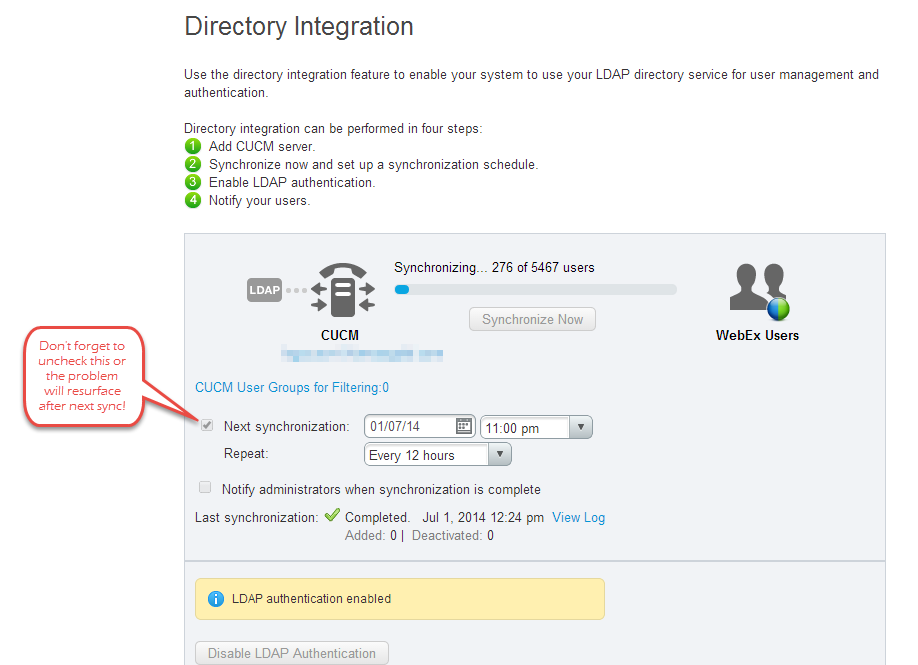
- Disable periodic synchronization.
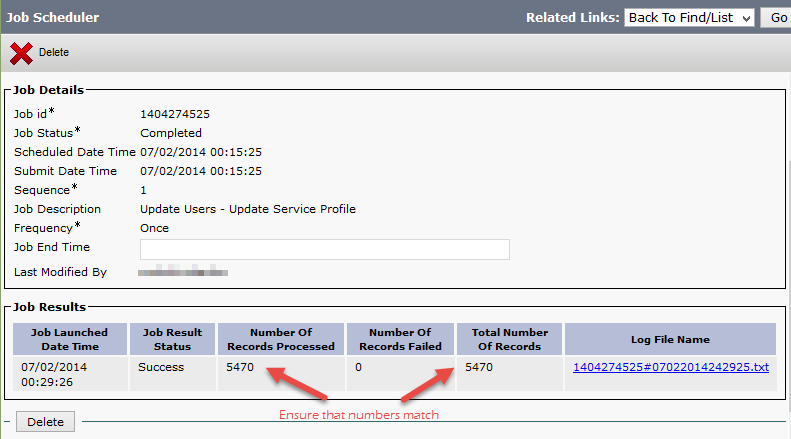
I found it easiest to bulk update user objects using a query (Bulk Administration -> Users -> Update Users -> Query). I have made a copy of an existing Service Profile and saved it under a different name, then switched all of my users to that Service Profile using a query in Bulk Administration. Use Job Scheduler to verify that all records have been updated successfully.
Once the batch job completes successfully and you have confirmed that all records have been updated, proceed with synchronization of users with CUCM in CWMS.
Important: Do not forget to disable periodic synchronization!
 Hope you did not have to go through this. I will update the post once a hotfix or an update with a fix becomes available. You can also save the bug CSCup62113 and add email subscription to receive updates on it in Cisco’s bug tracker tool.
Hope you did not have to go through this. I will update the post once a hotfix or an update with a fix becomes available. You can also save the bug CSCup62113 and add email subscription to receive updates on it in Cisco’s bug tracker tool.
VCS/Expressway Release X8.2 is here
The long-awaited X8.2 for VCS Control/Expressway and Expressway-Core/Expressway-Edge is finally available on the CCO for download. In this version of software Cisco re-introduces support for Jabber Guest (which has been officially promoted to production just a few days ago). Apart from support of Jabber Guest, the new release adds a few other perks:
- External XMPP Federation of CUPS-registered users with other deployments
- Ability to change RTP/RTCP media demultiplexing ports
- Better diagnostic logging and usability improvements in GUI
Please refer to the posted Release Notes for more details.
I the next few posts I will be covering deployment of Cisco Jabber Guest and MRA (Mobile Remote Access) for a small- to medium-size environment, so stay tuned.
New TMS Extension for MS Exchange 4.0.1
A new version of TMS Extension for Microsoft Exchange has been released today and is available for download from CCO. Some of the highlights of the newest version:
- Added support for MS Exchange 2013 (finally!), but with some limitations.
- Added support for Office 365 in technical preview (again, with some limitations).
- Added redundancy option, with TMSXE working in an active/passive cluster mode.
- Now the mailboxes can be added in batch (using CSV import), and it is no longer necessary to stop the TMSXE service when adding/removing mailboxes.
For more information, read the full Release Notes posted on Cisco’s website.
Sophos Anti-Virus Database Expired on Cisco IronPort ESA
Update: Looks like the problem has been resolved on May 16th at around 11:00pm EST.
So I got a new alert from our Cisco IronPort Email Security Appliances (ESAs) after midnight last night stating that the Anti-Virus database has expired. Here’s what the alert says:
The Warning message is:
sophos antivirus – The Anti-Virus database on this system is expired. Although the system will continue to scan for existing viruses, new virus updates will no longer be available. Please run avupdate to update to the latest engine immediately. Contact Cisco IronPort Customer Support if you have any questions.
Current Sophos Anti-Virus Information:
SAV Engine Version 4.97
IDE Serial 2014051602
Last Engine Update Thu May 15 15:23:44 2014
Last IDE Update Fri May 16 05:10:47 2014
Last message occurred 261 times between Fri May 16 07:10:43 2014 and Fri May 16 07:30:56 2014.
Now, I know that the feature key for Sophos Anti-Virus is valid for another couple of years (you can actually check that by logging in to your ESA’s GUI -> System Administration -> Feature Keys and verifying Feature Keys for your appliance), so the alert was completely misleading. After contacting Cisco TAC about the issue, we had a confirmation that the problem is on their end and that it will be resolved automatically once the Sophos engine is updated to verison 4.97 (via regular download to the appliance). No customer action is required. Cisco has actually released an advisory on their Support Community page about this issue, which you can read here: https://supportforums.cisco.com/community/5756/email-security.
Things happen. We’ll be patient.
Confirmed Vulnerabilities in Cisco WRF and ARF Players
Cisco has issued a new Security Advisory confirming vulnerabilities in its WebEx Recording Format (WRF) and Advanced Recording Format (ARF) Players. WebEx Business Suite (cloud) clients should upgrade their WebEx software client to the latest version. The following client builds of Cisco WebEx Business Suite (WBS27, WBS28, WBS29) and Cisco WebEx 11 correct these vulnerabilities:
- Cisco WebEx Business Suite (WBS29) client builds T29.2 or later
- Cisco WebEx Business Suite (WBS28) client builds T28.12 or later
- Cisco WebEx Business Suite (WBS27) client builds T27TLSP32EP16 (27.32.16) or later
- Cisco WebEx 11 version 1.2.10 with client builds T28.12 or later
- Cisco WebEx Meetings Server client builds 2.0.0.1677 or later
Client builds of the Cisco WebEx Business Suite prior to T27 SP32 have reached end of support; to obtain fixed software please upgrade to the latest version.
Cisco WebEx Meetings Servers (on-prem) clients should upgrade to version 2.0 or later (the most current version is 2.0 MR3).
To read the full Security Advisory go to http://tools.cisco.com/security/center/content/CiscoSecurityAdvisory/cisco-sa-20140507-webex.
A Few Words About Directory Integration in CWMS
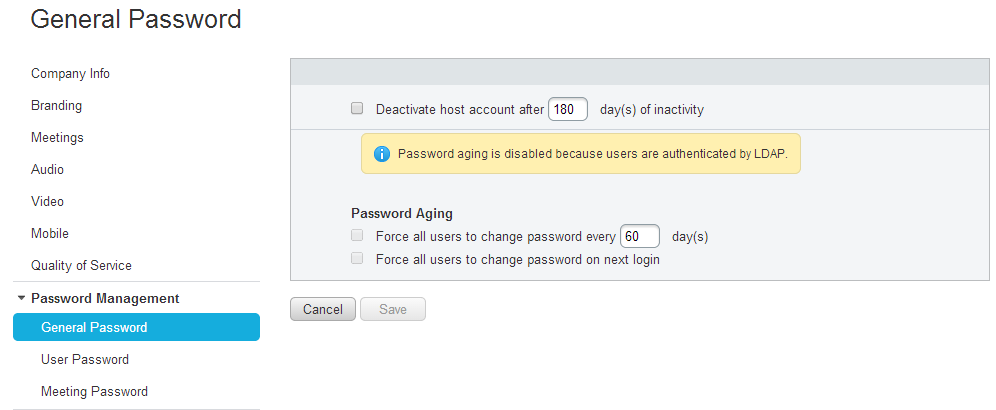
If your organization uses Cisco WebEx Meetings Server with AD directory and AD authentication and you have configured the Directory Integration according to the CWMS Administration Guide, you may be due for a surprise within a few months of initial configuration with a number of users being turned inactive. “But why?!” you ask. Remember that setting about password aging that supposedly does not apply to AD authenticated users? I’m talking about this one:
Well, turns out that if initially synchronized users did not login to CWMS within the default 180 days, their accounts get deactivated. Naturally, one would want to re-activate the accounts and, if you are dealing with a large number of users, you would almost always choose to activate in bulk using CSV file. A word of caution here: activating a large number of users with CSV import also triggers AD Activation Email to be sent out to all enabled users (even if the option to automatically notify users is unchecked under Users -> Directory Integration:
You may want to modify the AD Activation Email template (found under Settings -> Email -> Templates) or, if you prefer WebEx Meetings Server not to reach out to end users, configure a Hub Transport rule on your Exchange server to automatically discard or redirect messages with “Action Required: Activate account” in the Subject line. Which is precisely what I have done:
[PS] C:>New-TransportRule -Name "Disable CWMS AD Activation Email" -SubjectOrBodyContainsWords "Action Required: Activate account" -FromAddressContainsWords "cwms.ucpro.ca" -Comments "This rule disables AD Activation email from Cisco WebEx Meetings Server" -Enabled $true Name State Priority Comments ---- ----- -------- -------- Disable CWMS AD Activation Email Enabled 10 This rule disables AD Activation email from Cis...
I am not sure if disabling the password aging policy would prevent the active accounts from going inactive after 180 days (or some other value if different from default), but I recommend disabling the supposedly inapplicable password aging policy anyway.